MuleSoft for Financial Services: How to Secure Banking Data and Stay Compliant
Banks lose millions to data breaches from fragmented integrations. How MuleSoft for financial services replaces risky connections with governed, secure API architecture.
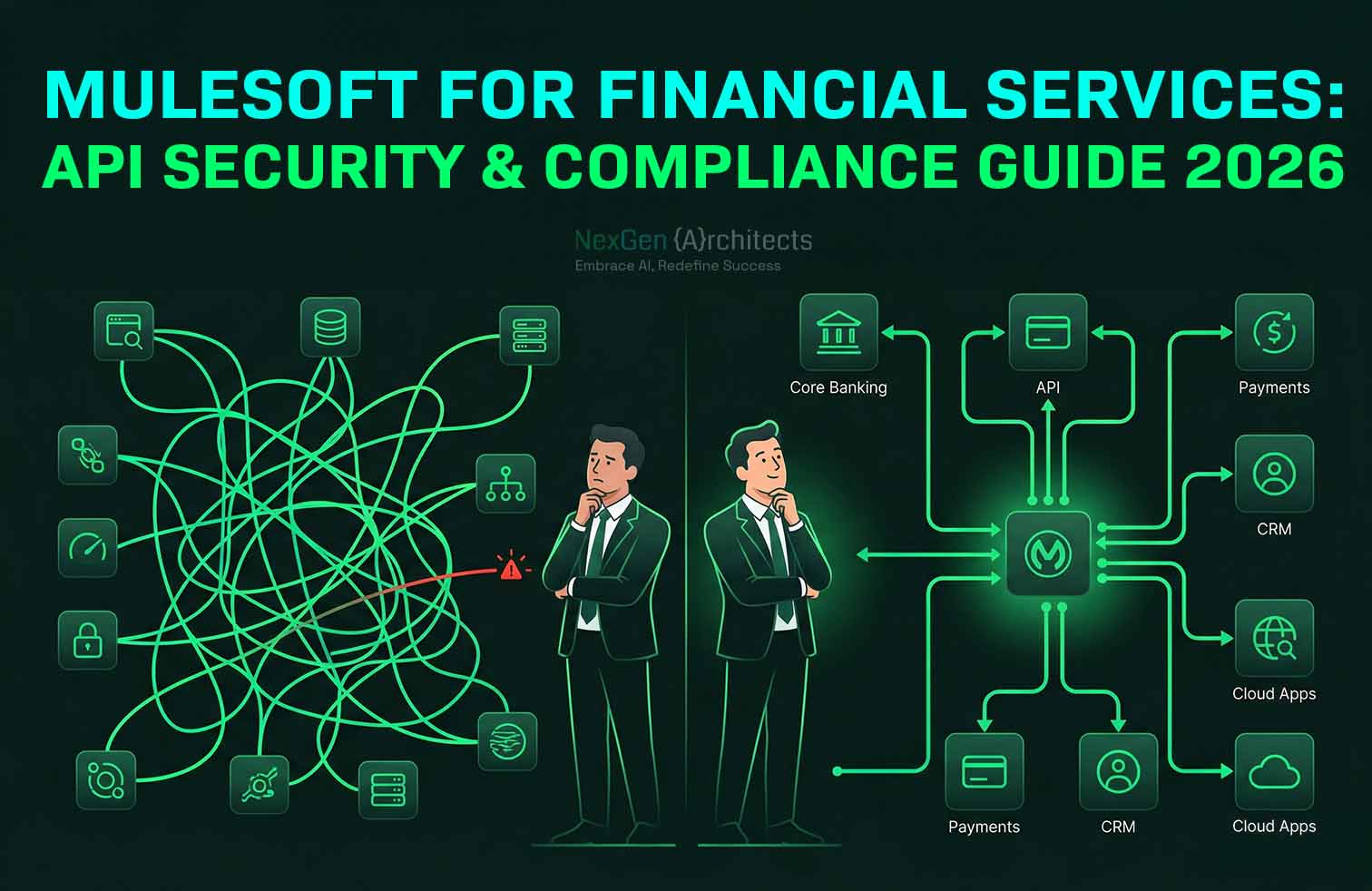
Most banks have hundreds of custom-built connections moving data between systems. A script here to sync customer records with the core ledger. Another one there to feed account data into the mobile app. A third connecting the wealth management platform to a reporting tool. Most of these were built years ago by people who have since left the company. None of them are documented. And none of them go through the security team.
Every one of those invisible connections is a potential way in for an attacker. If one gets compromised, there is often a direct path to the most sensitive customer records in the bank. Meanwhile, the security team does not even know the connection exists. That is the core problem MuleSoft for financial services solves. It replaces the tangle of undocumented, ungoverned data pipes with a single controlled layer where every connection is visible, authenticated, and monitored. This blog covers how that architecture works, why traditional setups fail, and how the same approach handles regulatory compliance without manual reporting.
Why Legacy Banking Integrations Fail at Security
Scale of API Attacks on Financial Services
The numbers are no longer theoretical. Thales recorded over 40,000 API security incidents across 4,000 monitored environments in the first half of 2025 alone. In the same period, the Indusface Banking and Financial Services report tracked 742 million attacks targeting financial services web and API applications, a 51 percent increase year over year. API-specific attacks surged 60 percent.
IBM's 2025 Cost of a Data Breach Report puts the average breach cost for financial institutions at $6.08 million, 22 percent higher than the cross-industry average. And Akamai's financial services study found that 88.7 percent of financial companies experienced an API attack in the prior 12 months.
These are not attacks on obscure systems. They target the APIs that handle payments, customer data, and partner integrations. The exact connections most banks leave ungoverned.
Why Firewalls Alone Cannot Protect Banking APIs
Traditional perimeter security treats all traffic behind the firewall as trusted. But APIs behave differently from web pages. They expose business logic directly. They grant access to database queries. And when a new API goes live without going through security review, it becomes an open door that no firewall can see.
Thales found that although APIs represent only 14 percent of overall attack surfaces, they attract 44 percent of advanced bot traffic. Attackers focus their most sophisticated tools on the connections that carry the most valuable data. If those connections are not centrally managed, they are not centrally protected.
How MuleSoft for Financial Services Closes Security Gaps
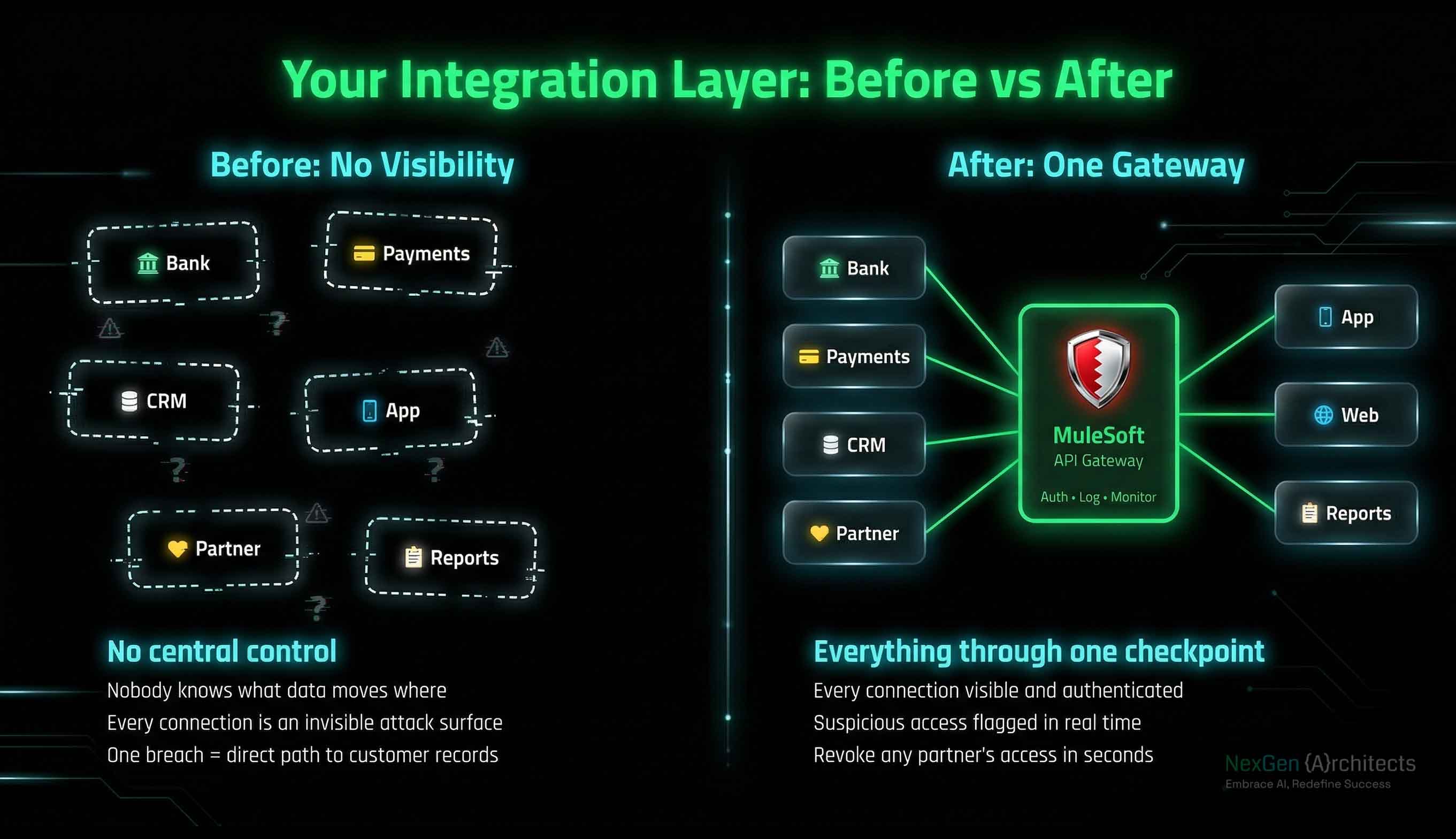
Centralizing Visibility Across All Data Flows
MuleSoft's Anypoint Platform works by routing all data traffic through a central gateway. Every API gets registered in a catalog. Every endpoint is visible. Every access request is tracked.
When a partner needs access to transaction data, you issue a token with specific permissions. The token defines what data they can pull, how frequently, and from which systems. If their access pattern changes unexpectedly, the platform flags it in real time.
This is the difference between chasing security problems after they happen and preventing them structurally. When every connection goes through a single checkpoint, nothing moves without being seen.
Catching Vulnerabilities Before They Ship
Anypoint Design Center moves security upstream into the design phase. Security rules get defined before any code is written. Automated pipelines scan every API specification for missing authentication, weak access controls, or exposed data fields.
If a new payment API is missing rate limiting, the pipeline catches it before it reaches a test environment. Problems get fixed at the blueprint stage instead of after a breach.
Hardening the MuleSoft API Gateway for Banking
Authentication, Encryption, and Tokenization
Anypoint API Manager lets you attach security policies directly to the gateway without modifying application code. A banking deployment typically layers these controls:
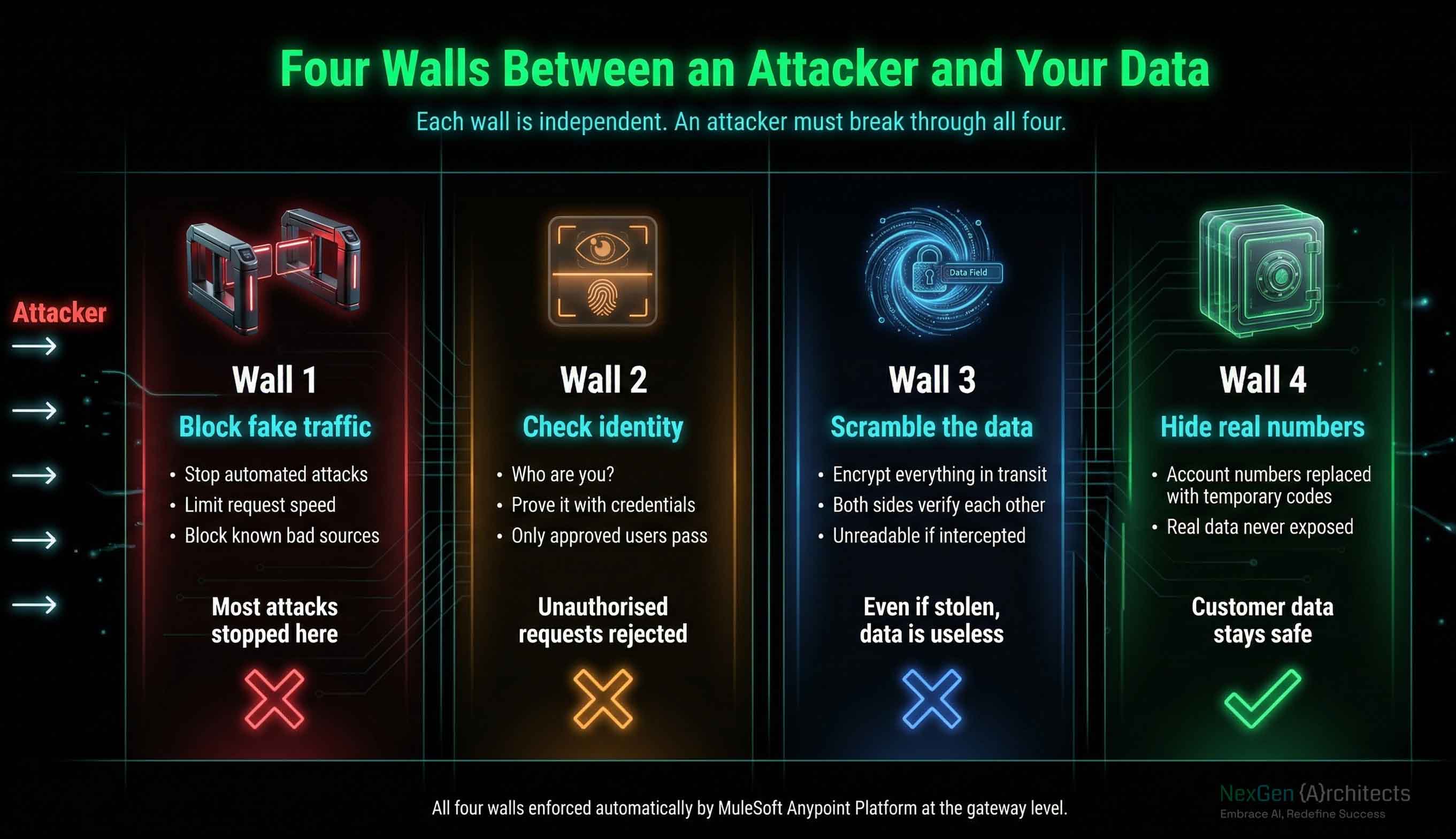
Edge protection
Gateways intercept all external traffic and enforce IP allowlists. Rate limiting prevents automated attacks from overwhelming endpoints.
Identity verification
OAuth 2.0 with OpenID Connect handles authentication for all external-facing APIs. Login credentials stay with a dedicated identity provider like Okta or Ping Identity, never touching the application layer.
Internal encryption
Mutual TLS between internal APIs and legacy databases ensures both sides verify each other before exchanging data. Even if an attacker reaches the internal network, they cannot read traffic without the correct certificates.
Data tokenization
Sensitive fields like account numbers and personal information get replaced with secure tokens at the gateway. Plain-text financial data never reaches logging systems, analytics tools, or partner integrations.
Isolating Failures to Prevent Cascading Outages
Mule 4's runtime engine isolates individual API workers. If one worker crashes or gets targeted, the rest of the application network stays stable. A failure in one connection does not bring down the entire integration layer.
Anypoint Virtual Private Cloud adds network-level isolation. IPsec VPN tunnels connect the MuleSoft runtime to on-premises data centers through encrypted channels. Data stays within protected corridors at every step.
Automating Financial Services Compliance with MuleSoft
Real-Time Audit Trails and Threat Detection
Compliance teams at most banks spend weeks before an audit pulling logs from scattered systems and manually tracing data flows. MuleSoft eliminates that scramble by centralizing all integration traffic through one platform.
Anypoint Monitoring records every transaction: who requested the data, which system provided it, when it happened, and what the payload contained. Auditors get instant access to tamper-evident dashboards instead of waiting for spreadsheets to be assembled.
Connecting Anypoint Platform to a SIEM tool like Splunk adds real-time alerting. If an IP address starts pulling thousands of account statements at unusual hours, the system flags it and blocks the source automatically. SQL injection attempts through an API get dropped at the gateway before they reach any database.
Meeting GDPR Data Residency Requirements
Banks operating in Europe must keep certain customer records within regional borders. MuleSoft CloudHub 2.0 lets you deploy runtimes in specific geographic regions. A European API connects to a European database. The global layer only sees aggregated, anonymized data. Customer records never cross borders because the architecture physically prevents it.
PCI DSS Segmentation Through API Architecture
PCI DSS requires strict separation between cardholder data and public-facing systems. API-led architecture provides that separation by design. Cardholder data stays locked in the system layer behind encryption and tokenization. Business logic APIs handle workflows without touching raw card numbers. Customer-facing APIs serve only tokenized references. You meet segmentation requirements through structure, not through bolt-on controls.
Replacing Legacy Middleware with Governed API Gateways
Strangler Pattern for Safe Migration
Ripping out legacy middleware overnight is not realistic when it touches every critical banking system. The strangler pattern takes a safer approach. You wrap the core banking ledger with a new secure API. Then you migrate old connections one at a time. Each point-to-point link gets replaced by a governed gateway connection. As traffic shifts to the new layer, the old system shrinks until it can be retired.
Preventing the Same Mess From Rebuilding Over Time
A Center of Excellence keeps the new architecture clean. This team sets the rules: approved API templates, security protocols, access policies. When a team wants to build a new feature, they use pre-approved patterns instead of writing another undocumented script. Standards get enforced before code is written.
Isolating Threats Without Shutting Down Services
When a partner reports a breach, you disable their API credentials in seconds. The rest of the network keeps running. No system-wide shutdown. No scrambling to figure out which connections that partner touches. Every connection is already visible and centrally managed.
Conclusion
The banks getting breached in 2026 are not getting breached because they lack security tools. They are getting breached because their integration layer is invisible, ungoverned, and impossible to monitor. Hundreds of custom connections built over decades, none of them documented, all of them carrying sensitive data.
MuleSoft for financial services replaces that architecture entirely. A single governed layer where every connection is visible. Every access request is authenticated. Every payload is encrypted or tokenized. And compliance reporting that takes minutes instead of weeks.
The financial institutions implementing this now are not just reducing breach risk. They are cutting the cost of compliance, accelerating audit readiness, and building an integration layer that can absorb new regulations without manual rework.
If you are evaluating your integration security or planning a middleware migration, talk to our architecture team for a free consultation.

.svg)

